HUAWEI防火墙通过IKE方式协商IPSec VPN隧道(采用预共享密钥认证)
上古南城 人气:0组网图形
组网需求
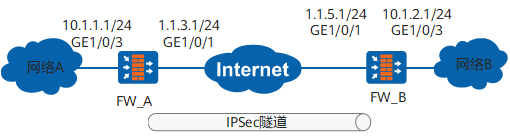
如图1所示,网络A和网络B分别通过FW_A和FW_B连接到Internet。网络环境描述如下:
- 网络A属于10.1.1.0/24子网,通过接口GigabitEthernet 1/0/3与FW_A连接。
- 网络B属于10.1.2.0/24子网,通过接口GigabitEthernet 1/0/3与FW_B连接。
- FW_A_B路由可达。
通过组网实现如下需求:在FW_A和FW_B之间建立IKE方式的IPSec隧道,使网络A和网络B的用户可通过IPSec隧道互相访问。
配置思路
对于FW_A和FW_B,配置思路相同。如下:
- 1.完成接口基本配置。
- 2.配置安全策略,允许私网指定网段进行报文交互。
- 3.配置到对端内网的路由。
- 4.配置IPSec策略。包括配置IPSec策略的基本信息、配置待加密的数据流、配置安全提议的协商参数。
操作步骤
1.配置FW_A的基础配置。包括配置接口IP地址、接口加入安全区域、域间安全策略和静态路由。
- 1.1 配置接口IP地址。
a.配置接口GigabitEthernet 1/0/3
<sysname> system-view [sysname] sysname FW_A [FW_A] interface GigabitEthernet 1/0/3 [FW_A-GigabitEthernet1/0/3] ip address 10.1.1.1 24 [FW_A-GigabitEthernet1/0/3] quit
b.配置接口GigabitEthernet 1/0/1的IP地址。
[FW_A] interface GigabitEthernet 1/0/1 [FW_A-GigabitEthernet1/0/1] ip address 1.1.3.1 24 [FW_A-GigabitEthernet1/0/1] quit
- 1.2 配置接口加入相应安全区域
a.将接口GigabitEthernet 1/0/3加入Trust区域。
[FW_A] firewall zone trust [FW_A-zone-trust] add interface GigabitEthernet 1/0/3 [FW_A-zone-trust] quit
b.将接口GigabitEthernet 1/0/1加入Untrust区域。
[FW_A] firewall zone untrust [FW_A-zone-untrust] add interface GigabitEthernet 1/0/1 [FW_A-zone-untrust] quit
- 1.3 配置域间安全策略。
a.配置Trust域与Untrust域之间的域间安全策略。
[FW_A] security-policy [FW_A-policy-security] rule name policy1 [FW_A-policy-security-rule-policy1] source-zone trust [FW_A-policy-security-rule-policy1] destination-zone untrust [FW_A-policy-security-rule-policy1] source-address 10.1.1.0 24 [FW_A-policy-security-rule-policy1] destination-address 10.1.2.0 24 [FW_A-policy-security-rule-policy1] action permit [FW_A-policy-security-rule-policy1] quit
[FW_A-policy-security] rule name policy2 [FW_A-policy-security-rule-policy2] source-zone untrust [FW_A-policy-security-rule-policy2] destination-zone trust [FW_A-policy-security-rule-policy2] source-address 10.1.2.0 24 [FW_A-policy-security-rule-policy2] destination-address 10.1.1.0 24 [FW_A-policy-security-rule-policy2] action permit [FW_A-policy-security-rule-policy2] quit
b.配置Local域与Untrust域之间的域间安全策略。
配置Local域和Untrust域的域间安全策略的目的为允许IPSec隧道两端设备通信,使其能够进行隧道协商。
说明:
本例中是以源地址和目的地址为例介绍,如果需要使用协议、端口作为匹配条件,则需要放开ESP服务和UDP 500端口(NAT穿越场景中还需要放开4500端口)。
[FW_A-policy-security] rule name policy3 [FW_A-policy-security-rule-policy3] source-zone local [FW_A-policy-security-rule-policy3] destination-zone untrust [FW_A-policy-security-rule-policy3] source-address 1.1.3.1 32 [FW_A-policy-security-rule-policy3] destination-address 1.1.5.1 32 [FW_A-policy-security-rule-policy3] action permit [FW_A-policy-security-rule-policy3] quit
[FW_A-policy-security] rule name policy4 [FW_A-policy-security-rule-policy4] source-zone untrust [FW_A-policy-security-rule-policy4] destination-zone local [FW_A-policy-security-rule-policy4] source-address 1.1.5.1 32 [FW_A-policy-security-rule-policy4] destination-address 1.1.3.1 32 [FW_A-policy-security-rule-policy4] action permit [FW_A-policy-security-rule-policy4] quit [FW_A-policy-security] quit
- 1.4 配置到达目的网络B的静态路由,此处假设到达网络B的下一跳地址为1.1.3.2。
[FW_A] ip route-static 10.1.2.0 255.255.255.0 1.1.3.2 [FW_A] ip route-static 1.1.5.0 255.255.255.0 1.1.3.2
2.在FW_A上配置IPSec策略,并在接口上应用此IPSec策略。
- 2.1 定义被保护的数据流。配置高级ACL 3000,允许10.1.1.0/24网段访问10.1.2.0/24网段。
[FW_A] acl 3000 [FW_A-acl-adv-3000] rule 5 permit ip source 10.1.1.0 0.0.0.255 destination 10.1.2.0 0.0.0.255 [FW_A-acl-adv-3000] quit
- 2.2 配置IPSec安全提议。缺省参数可不配置。
[FW_A] ipsec proposal tran1 [FW_A-ipsec-proposal-tran1] esp authentication-algorithm sha2-256 [FW_A-ipsec-proposal-tran1] esp encryption-algorithm aes-256 [FW_A-ipsec-proposal-tran1] quit
- 2.3 配置IKE安全提议。
[FW_A] ike proposal 10 [FW_A-ike-proposal-10] authentication-method pre-share [FW_A-ike-proposal-10] prf hmac-sha2-256 [FW_A-ike-proposal-10] encryption-algorithm aes-256 [FW_A-ike-proposal-10] dh group14 [FW_A-ike-proposal-10] integrity-algorithm hmac-sha2-256 [FW_A-ike-proposal-10] quit
- 2.4 配置IKE peer。
[FW_A] ike peer b [FW_A-ike-peer-b] ike-proposal 10 [FW_A-ike-peer-b] remote-address 1.1.5.1 [FW_A-ike-peer-b] pre-shared-key Test!1234 [FW_A-ike-peer-b] quit
- 2.5 配置IPSec策略。
[FW_A] ipsec policy map1 10 isakmp [FW_A-ipsec-policy-isakmp-map1-10] security acl 3000 [FW_A-ipsec-policy-isakmp-map1-10] proposal tran1 [FW_A-ipsec-policy-isakmp-map1-10] ike-peer b [FW_A-ipsec-policy-isakmp-map1-10] quit
- 2.6 在接口GigabitEthernet 1/0/1上应用IPSec策略组map1。
[FW_A] interface GigabitEthernet 1/0/1 [FW_A-GigabitEthernet1/0/1] ipsec policy map1 [FW_A-GigabitEthernet1/0/1] quit
3.配置FW_B的基础配置。包括配置接口IP地址、接口加入安全区域、域间安全策略和静态路由。
- 3.1 配置接口IP地址。
a.配置接口GigabitEthernet 1/0/3的IP地址。
<sysname> system-view [sysname] sysname FW_B [FW_B] interface GigabitEthernet 1/0/3 [FW_B-GigabitEthernet1/0/3] ip address 10.1.2.1 24 [FW_B-GigabitEthernet1/0/3] quit
b.配置接口GigabitEthernet 1/0/1的IP地址
[FW_B] interface GigabitEthernet 1/0/1 [FW_B-GigabitEthernet1/0/1] ip address 1.1.5.1 24 [FW_B-GigabitEthernet1/0/1] quit
- 3.2 配置接口加入相应安全区域。
a.将接口GigabitEthernet 1/0/3加入Trust区域。
[FW_B] firewall zone trust [FW_B-zone-trust] add interface GigabitEthernet 1/0/3 [FW_B-zone-trust] quit
b.将接口GigabitEthernet 1/0/1加入Untrust区域。
[FW_B] firewall zone untrust [FW_B-zone-untrust] add interface GigabitEthernet 1/0/1 [FW_B-zone-untrust] quit
- 3.3 配置域间安全策略。
a.配置Trust域与Untrust域之间的域间安全策略。
[FW_B] security-policy [FW_B-policy-security] rule name policy1 [FW_B-policy-security-rule-policy1] source-zone trust [FW_B-policy-security-rule-policy1] destination-zone untrust [FW_B-policy-security-rule-policy1] source-address 10.1.2.0 24 [FW_B-policy-security-rule-policy1] destination-address 10.1.1.0 24 [FW_B-policy-security-rule-policy1] action permit [FW_B-policy-security-rule-policy1] quit
[FW_B-policy-security] rule name policy2 [FW_B-policy-security-rule-policy2] source-zone untrust [FW_B-policy-security-rule-policy2] destination-zone trust [FW_B-policy-security-rule-policy2] source-address 10.1.1.0 24 [FW_B-policy-security-rule-policy2] destination-address 10.1.2.0 24 [FW_B-policy-security-rule-policy2] action permit [FW_B-policy-security-rule-policy2] quit
b.配置Untrust域与Local域之间的域间安全策略。
配置Local域和Untrust域的域间安全策略的目的为允许IPSec隧道两端设备通信,使其能够进行隧道协商。
[FW_B-policy-security] rule name policy3 [FW_B-policy-security-rule-policy3] source-zone local [FW_B-policy-security-rule-policy3] destination-zone untrust [FW_B-policy-security-rule-policy3] source-address 1.1.5.1 32 [FW_B-policy-security-rule-policy3] destination-address 1.1.3.1 32 [FW_B-policy-security-rule-policy3] action permit [FW_B-policy-security-rule-policy3] quit
[FW_B-policy-security] rule name policy4 [FW_B-policy-security-rule-policy4] source-zone untrust [FW_B-policy-security-rule-policy4] destination-zone local [FW_B-policy-security-rule-policy4] source-address 1.1.3.1 32 [FW_B-policy-security-rule-policy4] destination-address 1.1.5.1 32 [FW_B-policy-security-rule-policy4] action permit [FW_B-policy-security-rule-policy4] quit [FW_B-policy-security] quit
- 3.4 配置到达目的网络A的静态路由,此处假设到达网络A的下一跳地址为1.1.5.2。
[FW_B] ip route-static 10.1.1.0 255.255.255.0 1.1.5.2 [FW_B] ip route-static 1.1.3.0 255.255.255.0 1.1.5.2
4.在FW_B上配置IPSec策略,并在接口上应用此IPSec策略。
4.1 配置高级ACL 3000,允许10.1.2.0/24网段访问10.1.1.0/24网段。
[FW_B] acl 3000 [FW_B-acl-adv-3000] rule 5 permit ip source 10.1.2.0 0.0.0.255 destination 10.1.1.0 0.0.0.255 [FW_B-acl-adv-3000] quit
4.2 配置IPSec安全提议。
[FW_B] ipsec proposal tran1 [FW_B-ipsec-proposal-tran1] esp authentication-algorithm sha2-256 [FW_B-ipsec-proposal-tran1] esp encryption-algorithm aes-256 [FW_B-ipsec-proposal-tran1] quit
4.3 配置IKE安全提议。
[FW_B] ike proposal 10 [FW_B-ike-proposal-10] authentication-method pre-share [FW_B-ike-proposal-10] prf hmac-sha2-256 [FW_B-ike-proposal-10] encryption-algorithm aes-256 [FW_B-ike-proposal-10] dh group14 [FW_B-ike-proposal-10] integrity-algorithm hmac-sha2-256 [FW_B-ike-proposal-10] quit
4.4 配置IKE peer。
[FW_B] ike peer a [FW_B-ike-peer-a] ike-proposal 10 [FW_B-ike-peer-a] remote-address 1.1.3.1 [FW_B-ike-peer-a] pre-shared-key Test!1234 [FW_B-ike-peer-a] quit
4.5 配置IPSec策略。
[FW_B] ipsec policy map1 10 isakmp [FW_B-ipsec-policy-isakmp-map1-10] security acl 3000 [FW_B-ipsec-policy-isakmp-map1-10] proposal tran1 [FW_B-ipsec-policy-isakmp-map1-10] ike-peer a [FW_B-ipsec-policy-isakmp-map1-10] quit
4.6 在接口GigabitEthernet 1/0/1上应用IPSec策略组map1。
[FW_B] interface GigabitEthernet 1/0/1 [FW_B-GigabitEthernet1/0/1] ipsec policy map1 [FW_B-GigabitEthernet1/0/1] quit
结果验证
- 1.配置完成后,在PC1执行ping命令,触发IKE协商。若IKE协商成功,隧道建立后可以ping通PC2。反之,IKE协商失败,隧道没有建立则PC1不能ping通PC2。
- 2.分别在FW_A和FW_B上执行display ike sa、display ipsec sa会显示安全联盟的建立情况。以FW_B为例,出现以下显示说明IKE安全联盟、IPSec安全联盟建立成功。
<FW_B> display ike sa
IKE SA information :
Conn-ID Peer VPN Flag(s) Phase RemoteType RemoteID
-----------------------------------------------------------------------------
16777239 1.1.3.1:500 RD|ST|A v2:2 IP 1.1.3.1
16777232 1.1.3.1:500 RD|ST|A v2:1 IP 1.1.3.1
Number of IKE SA : 2
-------------------------------------------------------------------------------
Flag Description:
RD--READY ST--STAYALIVE RL--REPLACED FD--FADING TO--TIMEOUT
HRT--HEARTBEAT LKG--LAST KNOWN GOOD SEQ NO. BCK--BACKED UP
M--ACTIVE S--STANDBY A--ALONE NEG--NEGOTIATING
<FW_B> display ipsec sa
ipsec sa information:
===============================
Interface: GigabitEthernet1/0/1
===============================
-----------------------------
IPSec policy name: "map1"
Sequence number : 10
Acl group : 3000
Acl rule : 5
Mode : ISAKMP
-----------------------------
Connection ID : 83903371
Encapsulation mode: Tunnel
Tunnel local : 1.1.5.1
Tunnel remote : 1.1.3.1
Flow source : 10.1.2.2/255.255.255.255 0/0
Flow destination : 10.1.1.2/255.255.255.255 0/0
[Outbound ESP SAs]
SPI: 763065754 (0x2d7b759a)
Proposal: ESP-ENCRYPT-AES-256 SHA2-256-128
SA remaining key duration (kilobytes/sec): 0/3079
Max sent sequence-number: 1
UDP encapsulation used for NAT traversal: N
SA encrypted packets (number/kilobytes): 4/0
[Inbound ESP SAs]
SPI: 163241969 (0x9badff1)
Proposal: ESP-ENCRYPT-AES-256 SHA2-256-128
SA remaining key duration (kilobytes/sec): 0/3079
Max received sequence-number: 3203668
UDP encapsulation used for NAT traversal: N
SA decrypted packets (number/kilobytes): 4/0
Anti-replay : Enable
Anti-replay window size: 1024
加载全部内容